With the recent release of the trial transcripts for Ross Ulbricht, the man alleged to have run darknet marketplace Silk Road 1 as Dread Pirate Roberts, we’ve learned more of the catastrophically stupid decisions he made that ended up getting him caught. If you’re looking to run the next darknet market on Tor or I2P, here’s some basic OPSEC (Operations Security) and INFOSEC (Information Security) tips to keep you from making the same mistakes he did.
PROTIP #1: DO NOT KEEP A FUCKING CRIME DIARY
This seems obvious right? Ulbricht practically gift-wrapped himself for the FBI by making detailed notes on what he was doing. He had them in a “journal” directory and sorted by year, quarter, month, and week. The FBI could not have asked for a better proof of a criminal conspiracy. Didn’t he watch The Wire?
(Q is the attorney interviewing the witness, A, FBI agent Tom Kiernan)
He kept the diary out of his own vanity, thinking that he could swing a book deal. That’s arrogant, and horrendous OPSEC. Only ever take notes if you need to prove you WEREN’T responsible for something.
(This is a quote from Ulbricht’s detailed crime journal)
PROTIP #2: DO NOT USE YOUR REAL NAME ANYWHERE
Blake Benthall, DPR 2 of Silk Road 2, used his own private vanity address “blake@benthall.net” to register the server Silk Road 2 was hosted on. When the FBI started looking into the server, it was pretty easy to figure out who owned it:
(An excerpt from the FBI complaint against Blake Benthall)
Ulbricht didn’t fare any better. When he got started, he used “rossulbricht@gmail.com” to sign up and solicit people to help him make an “anonymous amazon.com” on a drug forum, and a Bitcoin forum. As he was an amateur with no coding experience, he signed up with his real name on Stack Overflow, a popular Q&A site for IT professionals. After he got some fucking sense, he changed his name to “frosty” and the email to “frosty@frosty,” which was the name of his user directory on his laptop.
PROTIP #3: LEARN TO CODE FIRST, THEN BUILD YOUR BLACK MARKET
Ulbricht was an amateur who only recently started coding. He asked very basic questions, with a Stack Overflow account linked to him, about how to make a PHP site that works on Tor, the question is still available on Stack Overflow.
(Excerpt from Ulbricht’s crime journal)
The FBI ended up finding the server because of a “leaky CAPTCHA.” CAPTCHAs are annoying wobbly letters you have to type to prove you’re not a robot. Ulbricht misconfigured his. The FBI were just typing random messages into a login to see where the replies were coming from and the CAPTCHA error message ended up going over the non-darknet. It was a trivial matter for the FBI to follow that back to the server.
As this was his first Bitcoin/Tor website, he initially manually processed the orders, jamming more and more fingerprints on his illicit Bitcoin activity, presumably for the FBI to enjoy. It wasn’t until the volume was high enough that he finally rewrote Silk Road to automate the dirty transactions.

(Excerpt from Ulbricht’s crime journal)
If you plan on making an e-commerce site, make sure it can do all the commerce parts automatically. There’s no reason to get your hands dirtier.
PROTIP #4: DO NOT LOG YOUR CHATS, DESTROY ALL LOGS
In order to keep anonymity, the Silk Road administrators used some manner of chat over Tor. There is TorChat, but it appears he logged all his chats. In fact, he kept 257 pages of logs discussing everything from customer complaints, to internal administrative discussions. Make sure everyone involved does not keep logs either.

(Q is the attorney interviewing the witness, A, FBI agent Tom Kiernan)
PROTIP #5: DON’T FUCKING WORK IN A PUBLIC PLACE
While Ross Ulbricht tried to keep his laptop encrypted, he was still working out of a public library. He was caught laptop open and decrypted by FBI agents faking a domestic dispute. When he stood up to take a peek, the agents snatched it away from him.

(Q is the attorney interviewing the witness, A, FBI agent Tom Kiernan)
Don’t trust spy or hacker movies. Hollywood INFOSEC says you need to be hopping around, using anonymous public Wi-Fi to hide your activities. But that leaves you vulnerable to an OPSEC fuckup like the FBI snatching the laptop off the table. It’s better to stay at home, hiding through Tor and anonymous VPNs, so if the FBI smash down your door, you have a second to slam your encrypted laptop shut.
PROTIP #6: DO NOT KEEP ANY IDENTIFYING INFORMATION OF ANYONE ELSE IN YOUR CONSPIRACY
A criminal conspiracy requires multiple people, and one thing you shouldn’t do, is keep scans of peoples’ drivers’ licenses.

(Excerpt from TorChat log presented as evidence in trial)
PROTIP #7: NEVER ACKNOWLEDGE THE CRIMINAL CONSPIRACY IN ANYTHING
If it wasn’t obvious before, regardless of your ideology, this is a crime. In anything you say, never acknowledge the name of it. Only speak in generalities and innuendo. This will make a lawyer’s job easier to introduce doubt into the jury’s mind.

(Excerpt from TorChat log presented as evidence in trial)
Everyone needs accounting, but Ulbricht kept it with the imaginative filename of “sr_accounting.ods”. It doesn’t take a genius to figure out what “sr” stands for.

(Q is the attorney interviewing the witness, A, FBI agent Tom Kiernan)
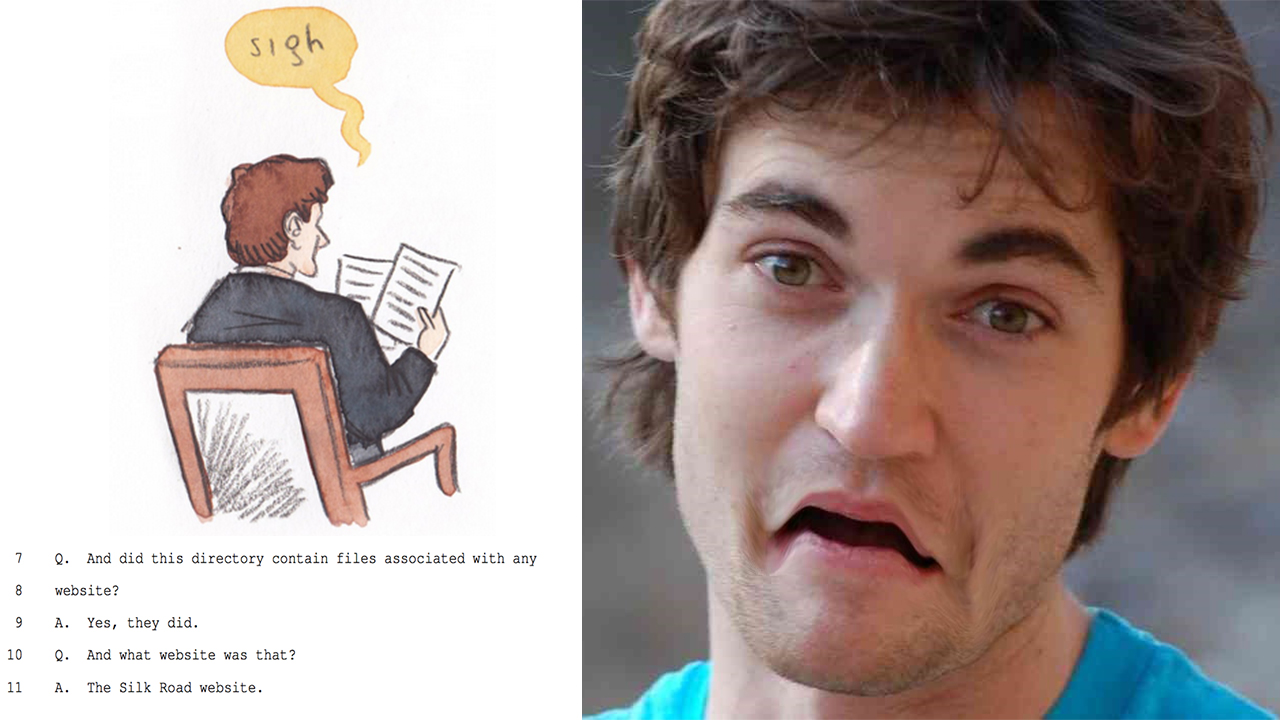
PROTIP #8: DO NOT KEEP AN ENTIRE COPY OF THE INCRIMINATING WEBSITE ON YOUR PERSONAL LAPTOP
Leave the development version on the remote server, leave the git repo or cvs directory on the remote server, because this gives you plausible deniability. Certainly don’t just keep an entire copy of it with you so the FBI can say, “nope, this is the guy who coded it, he had it all on him.”

(Q is the attorney interviewing the witness, A, FBI agent Tom Kiernan)